This Linux flaw could open you up to attack
A flaw in the Linux kernel lets hackers inject malware into downloads and webpages, smash Tor connections, launch denial-of-service attacks, and more.
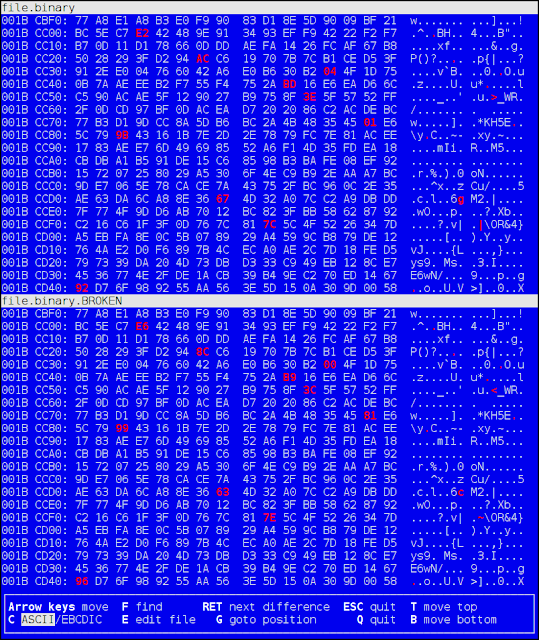
This sounds pretty serious. It sounds like if either side of a connection is affected by this bug, and an attacker knows both sides' IPs, then they can quickly confirm that a connection exists and insert whatever data they want into the middle of the connection. They can't read data sent between the two parties, though.
Where this is most worrying to me is system updates. On Linux, it's unfortunately fairly common for updates to be automatically delivered over HTTP and then not checked in a secure way. For example, Gentoo by default downloads packages insecurely, and on yum-based systems, even though the stock configuration is often secure, it's common to add insecure repos (for example, the official nginx repo is by default insecure). If your system downloads updates insecurely, then an attacker can maybe take over your computer by knowing just your IP address with this attack.
As a workaround while patches to fix the problem are prepared and distributed, you can raise the rate limit on your Linux machine or gadget so that it cannot be reached, by appending the following to /etc/sysctl.conf:
net.ipv4.tcp_challenge_ack_limit = 999999999
And then use sysctl -p to activate the new rule. You need to be root to do this.
Linux security backfires: Flaw lets hackers inject malware into downloads, disrupt Tor users, etc







Comments
Post a Comment